ts-scan available as github-action
Streamline Your Supply Chain Security: TrustSource’s ts-scan Now Available as a GitHub Action
We are thrilled to announce that TrustSource’s powerful Software Composition Analysis (SCA) tool, ts-scan, is now available directly within the GitHub Marketplace. Integrating robust security scanning and compliance into your CI/CD pipeline has never been easier.
The new ts-scan-action allows developers to automatically generate Software Bill of Materials (SBOMs) in standard formats—including SPDX and CycloneDX—directly within their workflows directly from the Github Marketplace.
Crucially, ts-scan is designed for simplicity and privacy. It operates entirely locally, meaning no API keys required for the basic actions and no data leaves your environment during the scan process, as long as you do not want to make use of the additional TrustSource SaaS offerings, such as risk management, automated legal compliance or approval flows. (learn more at https://www.trustsource.io )
Intelligent, Zero-Config Scanning
The unique selling proposition of ts-scan is its intelligent autodetection capability. Unlike many tools that require tedious configuration to define scope, ts-scan is capable of scanning almost all target types automatically without needing explicit direction.
Whether you are targeting common package management systems, specific files, entire repositories, or Docker images, ts-scan identifies the structure and performs the analysis seamlessly.
Get Started
Elevate your project’s transparency and security today by integrating TrustSource into your GitHub workflows.
-
Get the GitHub Action: Start using it immediately via the marketplace: https://github.com/trustsource/ts-scan-action
-
Deep Dive: Learn more about the tool’s extensive capabilities in our documentation: https://trustsource.github.io/ts-scan
-
Explore the Code: Check out the core tool repository on GitHub: https://github.com/trustsource/ts-scan
Update ts-scan to v1.5.2
Based on the events surrounding the Shai-Hulud worm, we have adjusted the basic configuration of our SCA scanner ts-scan. In its standard configuration, it no longer executes scripts from the <scripts> section of package.json. Instead, a warning is issued that there may be an insecure configuration. To execute the scripts anyway, the parameter node:enableLifecycleScripts must be explicitly added to the scan call from version 1.5.2 onwards.
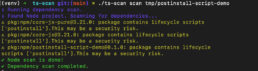
We recommend that our customers and users update ts-scan to the latest version – v1.5.2 in this case – to better protect their environment from malicious activity triggered by unwanted script execution.
PLEASE NOTE: This is not a vulnerability caused by ts-scan. The ability to embed arbitrary scripts in package.json and have them executed is a feature of the Node environment. This has existed for quite some time and was already discussed years ago as a potential security vulnerability. However, no action has been taken against it so far.

